top of page

Blog


Ransomware Attack on the Ombudsman Office: Critical Data at Risk
Financially motivated cyber attackers have launched a comprehensive ransomware attack against the IT infrastructure of the Irish Office of the Ombudsman. The institution, which urgently took all its systems offline to contain the threat, is considering the strong possibility that sensitive citizen data may have been exfiltrated by the hackers. Immediately following the incident, the National Cyber Security Centre and law enforcement agencies stepped in to launch a detailed fo
7 gün önce


Data Breach at Fintech Company Marquis: Hundreds of Thousands of Bank Customers at Risk
US-based financial technology provider Marquis has become the latest victim of ransomware gangs. The systems of the company, which provides marketing and compliance infrastructure to hundreds of banks and credit unions, were breached by exploiting a vulnerability in the firewall (SonicWall) they use. According to initial assessments of the attack, highly critical personal data such as names, addresses, dates of birth, credit card numbers, and social security numbers of more t
7 gün önce


Facilitating PCI DSS 4.0.1 Adoption
PCI DSS, the global security standard for card payment transactions, has become an urgent requirement for organizations with its updated version 4.0.1. This update, finalized in recent months, establishes a much clearer and stricter framework to address the increasing cyber risks in digital payments. Unlike previous versions, the new standard focuses not just on whether paper-based procedures are followed, but directly on whether data security is ensured. Companies are now re
7 gün önce


New Requirements for PCI DSS 4.0.1 and Digital Payment Security in 2025
With e-commerce volumes reaching trillions of dollars, the risk of cyberattacks is also increasing. The PCI DSS 4.0.1 standard, developed to protect credit card data against AI-powered attacks in particular, has become a critical requirement for organizations by 2025. New regulations, which came into effect in April, require companies to implement more sophisticated security measures. Many new technical controls are now mandatory, ranging from encrypting CVV codes and prevent
7 gün önce


The New Menace of Corporate Networks: Gentlemen Ransomware
The cybersecurity world is facing a new and ruthless ransomware group called "Gentlemen" that steals and encrypts companies' sensitive data. Emerging in August 2025, this gang, rather than attacking randomly, specifically targets medium and large-scale enterprises in critical sectors such as manufacturing, construction, and healthcare. Moving quite stealthily once it infiltrates the system, the software instantly disables security measures and data backup services before star
7 gün önce


Qilin Ransomware Attack on Pharmaceutical Research Giant Inotiv
U.S.-based major pharmaceutical research company Inotiv has announced that threat actors infiltrated their networks and compromised highly critical and personal data belonging to approximately 10,000 individuals. This massive data breach, which occurred last August and brought the company's daily operations to a standstill, was disclosed to the public through official notifications in December. The attack was claimed by the "Qilin" group, one of the most dangerous ransomware
7 gün önce

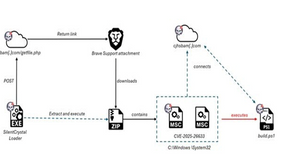
Russian Group EncryptHub Exploits MSC EvilTwin Vulnerability to Spread Fickle Stealer Malware
A hacker group known in the cybersecurity world as "EncryptHub," entirely driven by financial gain, continues to infiltrate corporate networks by exploiting a security vulnerability in Microsoft Windows systems. Combining technical manipulation with the power of persuasion (social engineering), this gang aims to infect companies' internal networks with malware that steals sensitive data from devices. The most striking aspect of the attack is that the hackers target company em
7 gün önce


Uncontrolled Secrets in DevOps Processes: Why PAM Systems Must Evolve?
Traditional Privileged Access Management (PAM) solutions are becoming increasingly inadequate in rapidly changing DevOps and cloud-based development environments. Under pressure to deploy projects faster, developers often embed API keys, cloud credentials, and tokens directly into code repositories. In the cybersecurity world, this creates a massive vulnerability known as "secrets sprawl." In the past, the breach of Uber's servers due to AWS keys left in a public GitHub repos
7 gün önce


The Latest Technology Trends Shaping the Jobs of the Future
In the business world, keeping up with new technology trends is no longer an option, but a critical necessity for survival and rapid career advancement. Companies are continuing their shift from traditional physical servers to cloud computing systems at an accelerating pace. Cloud technologies, offering flexibility, remote work capabilities, and significant cost advantages, are driving the demand for experts who can set up and maintain these complex systems to unprecedented l
7 gün önce


Cyberattacks on the Internet Archive
The Internet Archive is one of the most valuable treasures of the digital age. Established in 1996, this organization aims to leave a digital legacy for the future by archiving millions of web pages, digital books, movies, music, and more from the history of the internet. However, the preservation of digital archives faces a significant threat, especially from cyberattacks. In recent years, the Internet Archive has also encountered threats like DDoS (Distributed Denial of Ser
12 Kas 2024
bottom of page